| | Secure browsing is a high priority and a major interface challenge — specifically threats that are less detectable by the endusers, including phishing. We developed and tested a user-centered solution for phishing detection leveraging machine learning to implement personalized blocking, probabilistic logic for evidence fusion and risk communication for user empowerment. The proposed solution is implemented as a browser extension: the Holistic User-Centered Identificationof Threats (HUCIT). Our prototype provides immediate local identification of phishing websites and blocks unfamiliar scripts, based on machine learning threat detection and user risk perception.
|
 | | The current permissions models used by Android and iOS are not effective at communicating risk to the end user. Therefore, in the current mobile ecosystems, people rely on peer patterns of use, social feedback, ratings, and market reviews to choose between apps that offer the same functionality. However, this information does not include any details about over-privileging, use of resources, or corresponding risks. Our research group is focused on studying both the prevalence of over-permissioning and communicating risk to the end user.
|
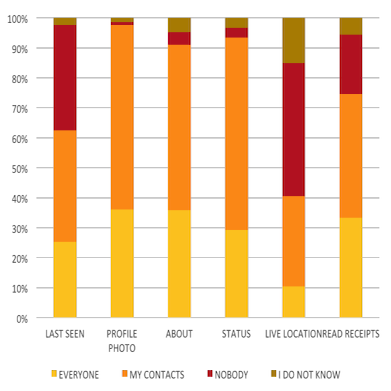
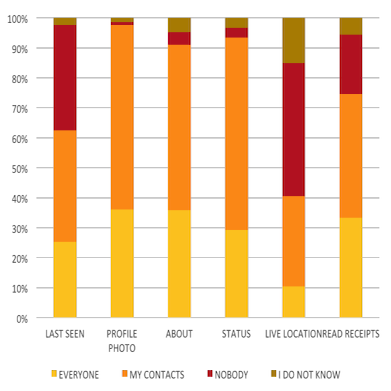 | | Our research project was a cultural study on WhatsApp users in India. WhatsApp is a mobile messaging platform that contains several privacy challenges, and a scope for better design in privacy communication. The largest population of mobile messaging applications users in India use WhatsApp, yet research on Indian perspectives, and non-western populations in general, towards privacy and security in such networking platforms is sparse. We queried privacy attitudes and behaviors of 213 Indian participants, using both open and closed-ended questions. Majority of participants reported that they actively use the privacy controls, on multiple data types, especially in group communications. Note that, in India groups are sometimes used for in schools and workplaces. We consider our findings and propose recommendations like including more refined access control in groups, better privacy communication and specific culturally sensitive privacy defaults.
|
 | | Passwords and Multi-Factor Authentication improve security and protect essential data of users online. However, the usage of simple and guessable passwords or compromised credentials often lead to several threats online, such as, Identity Theft, Financial Loss, etc. Irrespective of attacks, such as spear phishing attacks being present known for a long time, users still fall prey and sometimes fail to adapt to newer and safer technologies. One such technology is multi-factor authentication technology where in addition to passwords and username, users can authenticate through a second or third factor of authentication such as, One Time Passwords, SMSes, Tokens, Biometeric, etc. Our researchers investigate through detailed usability and adaptability research to understand user’s mental models and risk perception and unpack the difficulties an individual face to adapt such secure and helpful technologies. Several reasons contribute to lower security practices by an individual, including the ignorance or lack of knowledge of the users but also poor and transparent risk communication from security practitioners and organizations. Our user studies follow qualitative, quantitative, and mixed methods and provide actionable items and effective insights which contribute in improving the security practices of individuals and in turn enable protecting the online user data.
|
 | | The question that motivates this research is how to understand the interaction of the technical, organizational, and human factors that causes failures in Public Key Infrastructures (PKI). Next generation PKI should integrate a holistic understanding of human and organizational assumptions by design. We need better options for improving PKI in ways that protect privacy and address the contextual nature of trust, taking human behaviors and practices into account.
|
 | | The purpose of economics of security has been seen as an empirical and methodological way of understanding security technologies and behaviors. A profoundly different way of viewing economics of security is as a set of design constraints that can impinged acceptability and diffusion of a security protocol, tool, or system. Our research embeds all of these through macroeconomic analyses of ecrime, development of tools to mitigate risk, and using behavioral economics to incentivize individual users to improving the security of systems. Also embedded in our research is advocacy for a paradigm shift to thinking of security as a community resource, i.e., as `club goods' or `common-pool resources'.
|
 | | Concerns regarding the environment and the impact humans constantly have on the environment has been a growing concern for decades, but there is still a substantial lack of environmental literacy and action among most of the population in what they can do to reduce the damage they may be indirectly causing. The environmental impact of technology usage continues to garner attention as fears of built in obsolescence and high turn over of devices contribute to larger negative impacts. Our research aims at increasing environmental literacy and awareness along with giving users actionable steps and interactions to empower their control of individual carbon output and carbon footprints.
|
 | | Accurate communication of risk is not only an issue of high accuracy of underlying data but also in correctly designed simple communication. Past work on risk communication and usable privacy have focused primary on two cases: privacy risk via permissions in Android and security risks in browsing. Accurate feedback requires communication of risk, learning from the feedback, and aligning with user mental models.
|