| | Provide to people the security they need, the privacy they want, expressed with interactions they find acceptable. Reaching a secure state from the current state requires overcoming very serious gaps. This includes the gap between the cryptographic threat models and user risk preferences; the distance between cryptographic implementations and device capabilities; and between the usability of the devices in the home and expectations of the home’s occupants. The method was an introductory ground-setting keynote followed by intensive collaboration leveraging the participants’ collective expertise.
|
 | | Secure browsing is a high priority and a major interface challenge — specifically threats that are less detectable by the endusers, including phishing. We developed and tested a user-centered solution for phishing detection leveraging machine learning to implement personalized blocking, probabilistic logic for evidence fusion and risk communication for user empowerment. The proposed solution is implemented as a browser extension: the Holistic User-Centered Identificationof Threats (HUCIT). Our prototype provides immediate local identification of phishing websites and blocks unfamiliar scripts, based on machine learning threat detection and user risk perception.
|
 | | Manufacturer Usage Description (MUD) is a solution to defend Internet of Things (IoT) devices in home networks against cyber attacks. MUD uses the manufacturer's usage description to automatically setup a fine grained firewall on the network. Using MUD, the access of each device will be limited to the required domains and services, preventing an IoT device to get pwned or in case of a already-compromised IoT device, preventing it from communicating with outside servers or infecting other local IoT devices.
|
 | | The current permissions models used by Android and iOS are not effective at communicating risk to the end user. Therefore, in the current mobile ecosystems, people rely on peer patterns of use, social feedback, ratings, and market reviews to choose between apps that offer the same functionality. However, this information does not include any details about over-privileging, use of resources, or corresponding risks. Our research group is focused on studying both the prevalence of over-permissioning and communicating risk to the end user.
|
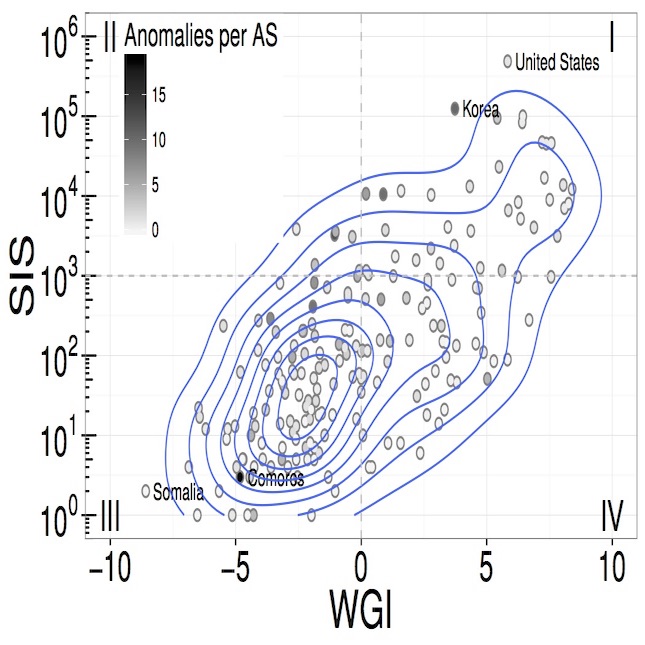
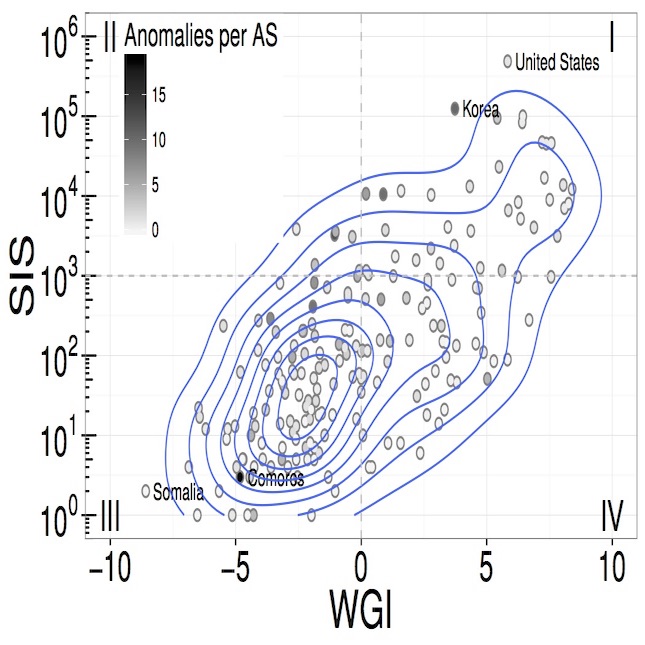 | | The Internet, as a network of networks, is also a network of trust. The most clear instantiation of that trust is the updating of router tables based on unsubstantiated announcements. The positive result of this trust is that the network can be extremely responsive to failures, and recovery quickly. Yet the very trust that enables resilience creates risks from behavior lacking either technical competence or benevolence. Threats to the control plane have included political interference, misguided network configurations, and other mischief. Our goal is to classify route updates along a continuum of trust, exploring new algorithms that will give a measure of integrity assurance to BGP updates. We will explore the application of machine learning techniques with the variety of data available (technical, rates of change, economic, and geopolitical) as network topology is changed via BGP updates in order to generate probabilistic (not cryptographic) trust indicators for those changes.
|
 | | Evaluating software quality and productivity is an open research challenge. In the past, expertise and ownership measures have shown to be effective in determining software quality, but most of the variance in software production can be neither consistently explained under our current measures in organizations. Past characterization of the individual actions of developers on software quality excludes the role of their interactions on overall performance. Yet, the intrinsically temporal nature of interactions create different collective behaviors that need to be understood in the light of failure data. Our goal is to characterize the collective character of software developers and its relationship to software failures. There is evidence suggesting that the improvement of software quality reduces the number of security vulnerabilities enhancing software security. We will explore the use of new algorithms that take into account the inner social structure of developers, ones that measure organizational context, to measure the integrity of their interactions with software components. In particular, we will apply a range of graph and data analytics techniques with a variety of data available (intrinsic characteristics of developers and software components, failures by components, and temporal logs of interactions) to evaluate the efficacy of graph topology in generating probabilistic trust indicators for the code resulting from these interactions. The proposed analysis will allow to understand the necessary conditions for addressing security vulnerabilities (as those posed by insiders) improving software quality.
|
 | | The question that motivates this research is how to understand the interaction of the technical, organizational, and human factors that causes failures in Public Key Infrastructures (PKI). Next generation PKI should integrate a holistic understanding of human and organizational assumptions by design. We need better options for improving PKI in ways that protect privacy and address the contextual nature of trust, taking human behaviors and practices into account.
|
 | | Aging in place means people living in their homes as long as possible as they age. Our early work in aging in place focused on the IoT as grounded in design for elders at home. It has two core projects: our current IoT project and our previous ETHOS project.
|
 | | Concerns regarding the environment and the impact humans constantly have on the environment has been a growing concern for decades, but there is still a substantial lack of environmental literacy and action among most of the population in what they can do to reduce the damage they may be indirectly causing. The environmental impact of technology usage continues to garner attention as fears of built in obsolescence and high turn over of devices contribute to larger negative impacts. Our research aims at increasing environmental literacy and awareness along with giving users actionable steps and interactions to empower their control of individual carbon output and carbon footprints.
|
 | | Accurate communication of risk is not only an issue of high accuracy of underlying data but also in correctly designed simple communication. Past work on risk communication and usable privacy have focused primary on two cases: privacy risk via permissions in Android and security risks in browsing. Accurate feedback requires communication of risk, learning from the feedback, and aligning with user mental models.
|
 | | What are the challenges, threats, implications and potential for SDN in terms of creating a resilient network? To answer this question, we have created clear threat models grounded in documented and realistic use cases; extracted resulting enumerated authentication requirements; implemented one case of the necessary next-generation network modeling to evaluate authentication interactions, such that the models address all layers from physical to human; and finally the demonstrated practical forward movement to meeting these challenges as an open source network component named Bongo.
|